In a recent LinkedIn post, I provided 4 suggestions as to how organisations can secure their remote workers, a thing I’m sure most would agree is of paramount importance under circumstances.
Of the 4 suggestions, I have already written blog posts that look in more detail at Azure Information Protection and Conditional Access, leaving me with just 2 more to cover. This week, I am going to be looking at the commonly known but under used Multi Factor Authentication (MFA).
Let’s Jump straight in…
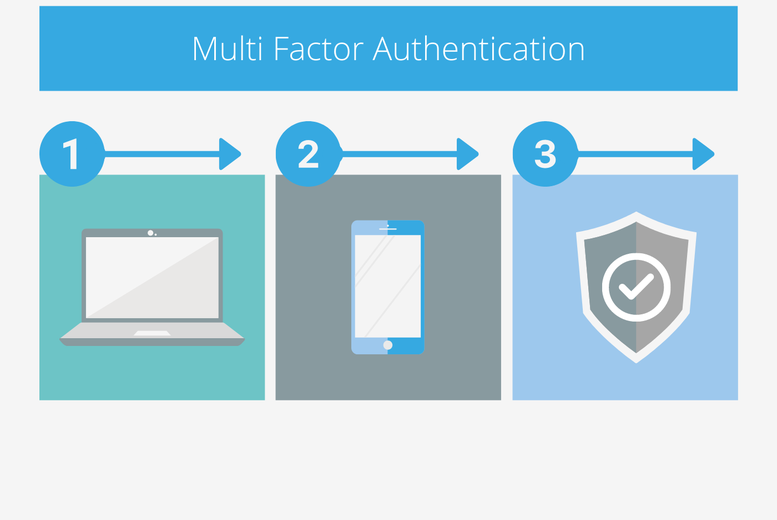
More and more organisations are choosing to implement MFA as a mandatory step in their login procedures. Most people these days will be aware of what MFA is and how it works, but for those who aren’t, you might have noticed that your bank and/or other such data storing giants have started sending you a text with a code you need to input in order to log in. Well, that’s MFA. By more formal definition, it is the requirement for a user to present 2 or more pieces of information to evidence authentication.
When we look at some of the information security numbers associated to MFA, it becomes clear as to why it’s so widely regarded. There are many statistics that I could reference here, but there is one that basically tells you everything you need to know. According to Microsoft, in an age where weak, default or stolen passwords are the cause of most data breaches, MFA can prevent 99.9% of attacks on your account. It’s almost unbelievable that such a simple step can be so effective. To achieve such a level of security, it seems more conceivable that we would need some intricate and expensive MoD level of protection. But no. It’s often the most basic steps that can protect us.
Sounds great… But how do I get it?...
The great thing is that Microsoft enforce MFA for admins on Office 365 accounts by default, providing that Security Defaults is enabled (there will be a follow up blog on Security Defaults in the near future). Doing this is a strong first step to protecting your environment. In addition to this, MFA is available and free with all Office 365 plans. That said, without the higher-level plans, it must be enforced manually for the users in a basic ‘on/off’ type scenario. The Circle Cloud video below will show you how you can do this…
It is at this point that I am going to take a step back a little. Remember how I said at the beginning of this post that MFA was ‘under used’. Well, it is this ‘on/off’ functionality that, although useful, creates some of the perceived problems. The reason for this is that many end users find it annoying when they have to put in a code every time they attempt to gain access to their devices.
So, what can be done to overcome this potential issue…
To answer this question, I am going to pose to you what is on offer as standard as part of all Microsoft Office 365 licenses, then present an alternative:
On offer as standard: I can manually enforce MFA for all users, meaning they must always input a code every time they try to access company assets.
Alternative: I would like to be able to apply MFA to all users, but for the users to only be asked to MFA in particular, pre-determined scenarios where I think it’s most needed (such as when accessing from a remote location and/or an insecure device).
Well, if you’ve come this far, you’ll be glad to know that the ‘alternative’ is certainly achievable if MFA is used in conjunction with Conditional Access. I recently wrote a blog post about Conditional Access which might be worth reading if you want to fully understand how the two link together. However, the brief overview below should get you started.
Using MFA as part of your Conditional Access Strategy…
For those who’ve never heard of conditional access, you can probably take a reasonable guess as to what it does. It restricts access to an organisation’s platforms and data by enforcing standards that must be met by a device or network before accessing information. The most simple takeaway message I can give you here is that Conditional Access allows you to decide what a compliant device looks like for your organisation, then gives you the power enforce rules on any ‘non-compliant’ devices trying to access company information and systems.
Conditional Access does this by applying basic ‘IF-THEN’ logic. I have provided an example below to give you an idea:
IF: a ‘non-compliant’ device attempts to log on
THEN: allow access through but only through a browser, and do not allow the user to download company information onto their ‘non-compliant’ device.
You might already have guessed by now where MFA fits into the picture. For obvious reasons, a lot of the restrictions that organisations apply to their policies are focussed on the enforcement of MFA, such as making it a mandatory requirement for anyone in the business who has administrative access. To put this into perspective, here is how the previously used ‘IF-THEN’ example would look if we used MFA as our rule to apply to non-compliant devices:
IF: a ‘non-compliant’ device attempts to log on
THEN: force the user to MFA
If you want to understand more about how Conditional Access works, Click Here. It will take you to a blog where you can watch a recent webinar recording where we looked at Conditional Access.
Final Remarks
MFA is an incredibly effective step to take in protecting our users (and organisations) against some of the most common information security threats of our age. Many IT teams don’t implement it as standard because of the pushback they get when their users complain about how irksome it can be to go through the MFA process over and over again. It’s easy for me to advise decision makers not to succumb to the pressure, however I appreciate that the reality is much different. That’s why a more realistic way to approach your MFA strategy may be to use it in conjunction with Conditional Access. By creating specific, scenario-based policies that only ask the user or user group to MFA when appropriate, we can create a sense of balance that benefits a user’s experience without compromising on security.
Get in touch if you would like to talk to Circle Cloud about how we can make Conditional Access and MFA work for your organisation.